A range check is used to check that a value input is above 10 and below 20.
Tick (✓) one box to show which value would be accepted.
10
15
20
30
Was this exam question helpful?
Exam code: 0478 & 0984
A range check is used to check that a value input is above 10 and below 20.
Tick (✓) one box to show which value would be accepted.
10
15
20
30
Choose your answer
Was this exam question helpful?
Verification checks can be made on input data.
Tick (✓) one box to show which check is a verification check on input data.
checksum
double entry check
echo check
parity check
Choose your answer
Was this exam question helpful?
Tick (✓) one box in each row to identify if the statement is about validation, verification or both.
Statement | Validation | Verification | Both |
|---|---|---|---|
Entering the data twice to check if both entries are |
|
|
|
Automatically checking that only numeric data has |
|
|
|
Checking data entered into a computer system |
|
|
|
Visually checking that no errors have been |
|
|
|
How did you do?
Was this exam question helpful?
Tick (✓) one box to complete this sentence.
A validation check to make sure that an email address contains an ‘@’ sign is a
Range check
Visual check
Presence check
Format check
Choose your answer
Was this exam question helpful?
Describe the purpose of validation and verification checks during data entry.
Include an example for each.
How did you do?
Was this exam question helpful?
A programmer has written an algorithm to check that prices are less than $10.00
These values are used as test data:
10.00 9.99 ten
State why each value was chosen as test data.
10.00
9.99
ten
How did you do?
Was this exam question helpful?
A program checks if the weight of a baby is at least 2 kilograms.
Give, with reasons, two different values of test data that could be used for the baby’s weight.
Each reason must be different.
How did you do?
Was this exam question helpful?
Give one piece of normal test data and one piece of erroneous test data that could be used to validate the input of an email address.
State the reason for your choice in each case.
How did you do?
Was this exam question helpful?
An algorithm allows a user to input their password and checks that there are at least eight characters in the password. Then, the user is asked to re-input the password to check that both inputs are the same. The user is allowed three attempts at inputting a password of the correct length and a matching pair of passwords.
The pre-defined function LEN(X) returns the number of characters in the string, X
01 Attempt ← 0 02 REPEAT 03 PassCheck ← TRUE 04 OUTPUT "Please enter your password " 05 INPUT Password 06 IF LEN(Password) < 8 07 THEN 08 PassCheck ← TRUE 09 ELSE 10 OUTPUT "Please re-enter your password " 11 INPUT Password2 12 IF Password <> Password 13 THEN 14 PassCheck ← FALSE 15 ENDIF 16 ENDIF 17 Attempt ← Attempt + 118 UNTIL PassCheck OR Attempt <> 3 19 IF PassCheck 20 THEN 21 OUTPUT "Password success" 22 ELSE 23 OUTPUT "Password fail" 24 ENDIF
Give two sets of test data for this algorithm and a reason for choosing each set.
Each set of test data and its reason must be different.
How did you do?
Was this exam question helpful?
Describe what is meant by data validation
How did you do?
Was this exam question helpful?
A validation check is used to make sure that any value that is input is an integer between 30 and 200 inclusive.
Give one example of each type of test data to check that the validation check is working as intended. Each example of test data must be different.
Give a reason for each of your choices of test data.
Normal test data
Abnormal test data
Extreme test data
How did you do?
Was this exam question helpful?
A program needs to make sure the value input for a measurement meets the following rules:
the value is a positive number
a value is always input
the value is less than 1000
Describe the validation checks that the programmer would need to use.
How did you do?
The program needs editing to include a double entry check for the value input
State why this check needs to be included.
How did you do?
Was this exam question helpful?
This pseudocode algorithm is intended to allow, at random, between 1 and 20 values to be entered and totalled. The total and average of the entered values are output at the end of the algorithm.
01 DECLARE Loop : INTEGER
02 DECLARE Limit : INTEGER
03 DECLARE Value : REAL
04 DECLARE Total : REAL
05 Total 0
06 Limit ROUND(RANDOM() * 19,0) + 1
07 FOR Loop 1 TO Limit
08 OUTPUT "Enter a number"
09 INPUT Value
10 Total Total + Value
11 NEXT Loop
12 OUTPUT "The total of the numbers entered is ", Total
13 OUTPUT "The average number entered is ", Total / LimitExplain how you should alter the algorithm to make sure that all the numbers entered are between 1 and 500 inclusive.
If any numbers fall outside these limits, a replacement value is requested and entered.
You do not need to re-write the algorithm.
How did you do?
Was this exam question helpful?
This flowchart represents an algorithm.

The array Name[1:4] used in the flowchart contains the following data:
|
|
|
|
|---|---|---|---|
|
|
|
|
Complete the trace table using the data given in the array
|
|
|
|
|
|
|
|---|---|---|---|---|---|---|
|
|
|
| |||
How did you do?
Was this exam question helpful?
This flowchart inputs the weight of items, in kilograms, to be loaded on a trailer. Any item over 25 kilograms is rejected. The trailer can take up to 100 kilograms.

Complete the trace table for the input data:
13, 17, 26, 25, 5, 10, 15, 35, 20, 15
|
|
|
|
|---|---|---|---|
How did you do?
Was this exam question helpful?
The pseudocode represents an algorithm.
The pre-defined function DIV gives the value of the result of integer division. For example, Y = 9 DIV 4 gives the value Y = 2
The pre-defined function MOD gives the value of the remainder of integer division. For example, R = 9 MOD 4 gives the value R = 1
First ← 0 Last ← 0 INPUT Limit FOR Counter ← 1 TO Limit INPUT Value IF Value >= 100 THEN IF Value < 1000 THEN First ← Value DIV 100 Last ← Value MOD 10 IF First = Last THEN OUTPUT Value ENDIF ENDIF ENDIF NEXT Counter
Complete the trace table for the algorithm using this input data:
8, 66, 606, 6226, 8448, 642, 747, 77, 121
|
|
|
|
|
|
|---|---|---|---|---|---|
How did you do?
Was this exam question helpful?
An algorithm allows a user to input their password and checks that there are at least eight characters in the password. Then, the user is asked to re-input the password to check that both inputs are the same. The user is allowed three attempts at inputting a password of the correct length and a matching pair of passwords.
The pre-defined function LEN(X) returns the number of characters in the string, X
01 Attempt ← 0 02 REPEAT 03 PassCheck ← TRUE 04 OUTPUT "Please enter your password " 05 INPUT Password 06 IF LEN(Password) < 8 07 THEN 08 PassCheck ← TRUE 09 ELSE 10 OUTPUT "Please re-enter your password "11 INPUT Password2 12 IF Password <> Password 13 THEN 14 PassCheck ← FALSE 15 ENDIF 16 ENDIF 17 Attempt ← Attempt + 1 18 UNTIL PassCheck OR Attempt <> 3 19 IF PassCheck 20 THEN 21 OUTPUT "Password success" 22 ELSE 23 OUTPUT "Password fail" 24 ENDIF
The algorithm includes two types of check on the data input.
Identify and describe each type of check.
How did you do?
Was this exam question helpful?
This algorithm checks the temperature of hot food being served to customers.

Complete the trace table for the algorithm using this input data:
75, 78, 84, 87, 91, 80, 75, 70, 65, 62, –1, 20
|
|
|
|
|
|
|
|---|---|---|---|---|---|---|
How did you do?
Was this exam question helpful?
The flowchart represents an algorithm.
![Flowchart starts at 'Start', initializes 'Pointer' to 1, inputs 'Letter', compares it with 'Word[Pointer, 1]', outputs a message, asks for another letter, loops or stops.](https://cdn.savemyexams.com/cdn-cgi/image/f=auto,width=3840/https://cdn.savemyexams.com/uploads/2024/09/25915_june-2022-21-qp-7a.png)
The table represents the two-dimensional (2D) array Word[] which stores the first half of the phonetic alphabet used for radio transmission. For example, Word[10,1] is ‘J’.
|
|
|
|---|---|---|
1 | A | Alpha |
2 | B | Bravo |
3 | C | Charlie |
4 | D | Delta |
5 | E | Echo |
6 | F | Foxtrot |
7 | G | Golf |
8 | H | Hotel |
9 | I | India |
10 | J | Juliet |
11 | K | Kilo |
12 | L | Lima |
13 | M | Mike |
Complete the trace table for the algorithm by using the input data: F, Y, D, N
|
|
|
|
|---|---|---|---|
How did you do?
Was this exam question helpful?
This flowchart represents an algorithm.

The array X[1:5] used in the flowchart contains this data:
|
|
|
|
|
|---|---|---|---|---|
10 | 1 | 5 | 7 | 11 |
Complete the trace table by using the data given in the array.
|
|
|
|
|
|
|
|
|---|---|---|---|---|---|---|---|
10 | 1 | 5 | 7 | 11 | |||
How did you do?
Was this exam question helpful?
The flowchart represents an algorithm.
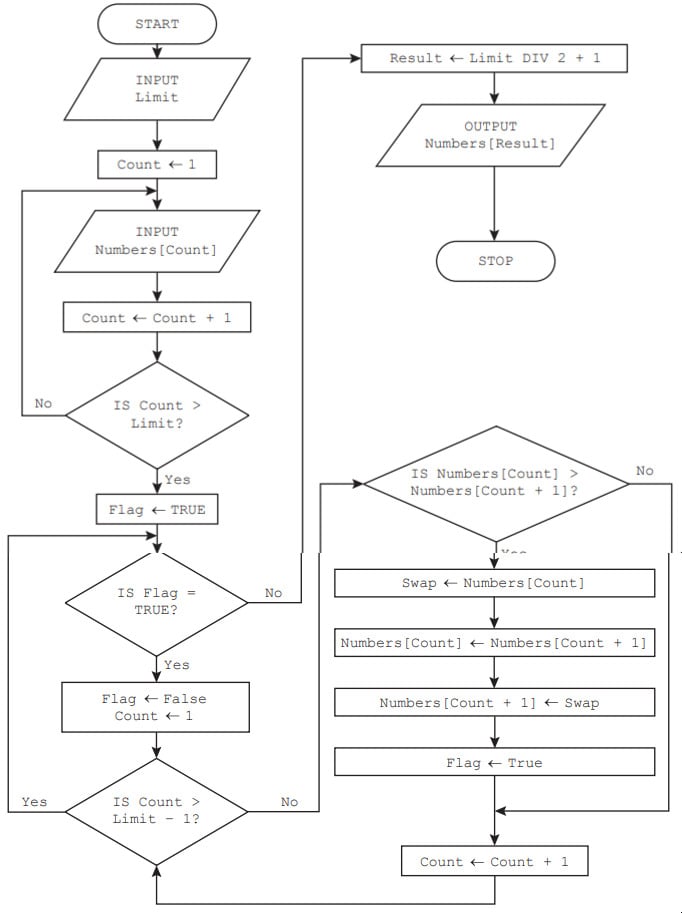
Complete the trace table for the input data:
7, 47, 50, 52, 60, 80, 63, 70
![A blank table with columns titled: Limit, Count, numbers [1] to [7], Flag, Swap, Result, and Output, intended for data entry or analysis.](https://cdn.savemyexams.com/cdn-cgi/image/f=auto,width=3840/https://cdn.savemyexams.com/uploads/2025/06/59002_0478-s24-qp-21-q6a-3.png)
How did you do?
Was this exam question helpful?